Six Tips to Mitigate Cyber Threats In The Workplace
There are over four billion users of the internet worldwide, which is about 1.5 billion more users than five years ago. While this increase has been good for e-commerce, it hasn’t been great for security or privacy. Cyber threats have unsolicited themselves as the inevitable nuisance of everyday life, making it more important than ever for companies to implement best practices for mitigating cyber threats. By following these six tips, you can mitigate threats in your business.
Host an Employee Security Awareness Training Program
Employees at all levels of a company can be targeted in a hack. For this reason, it is important that your company hosts an employee security awareness program regularly, for every employee throughout your organization so they are aware of the latest threats. The program should include case studies of hacks involving employees, steps to take when dealing with suspicious email or software, how to spot a phishing email, tips for online safety, and educating employees on what to do if they identify a suspicious threat. Once you develop the program—practice, practice, practice! The threat landscape is consistently evolving, staying up to date on the latest threats and educating your team about them can help!
Stay on Top of Security Updates
Be sure to stay up to date with operating system and software patches to secure vulnerabilities that could be exploited by hackers. Security flaws act as a low hanging fruit for hackers. Once hackers have identified the flaw on a network, they will target that vulnerability and infect it with malware. However, when these flaws and vulnerabilities are patched and updated, it will help protect from emerging threats. Our blog is a great resource to get the most up-to-date news in security from our Security Analytics Team.
Segment the Network
Segmenting your network will enhance security. It is recommended to segment the business network from the guest or public Wi-Fi networks, which limits threat exposure by not sharing traffic. This means if a PC is compromised on your guest network, the hacker will not have access to data in your business segment.
Create a Strict “Bring your own Device” (BYOD) Policy
Restrict the use of personal USB drives, external hard disks, thumb drives and writable media at your company, as they facilitate security breaches coming into or leaving your network. For example, if a PC is used in a non-secure environment, it can easily get hacked. When that PC is then connected to your network it can introduce that malware to your company network if it does not have proper security safeguards in place.
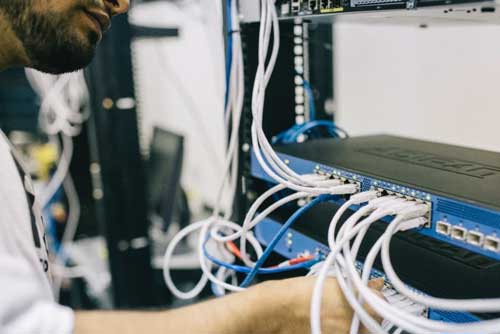
Physical Safeguards
The server and network room should be physically secured with limited access. Access should be limited to management and security professionals. The computers that run the software for the PoS terminals can be compromised with malicious code to capture credit card data—ensure these are secured and being monitored.
Outsource Managed Security Services Provider for Assistance
The last and final step is to partner with a managed security services provider (MSSP) to manage, monitor and respond to threats in real-time. Because the threat landscape is so complex, it’s nearly impossible to monitor every event entering a network. At Nuspire, our real-time threat monitoring leverages advanced managed detection and response capabilities, that overall lowers support costs, helps drive the company revenue and gives great optimization of internal resources.
To learn more about these steps to mitigate threats or if you’re interested in partnering with an MSSP for MDR services, contact a representative from Nuspire today!