Endpoint Detection and Response: To DIY or Not to DIY?
Dissecting EDR
Many organizations struggle with DIY endpoint detection and response (EDR), and stakeholders may question its efficacy and value. The usual path to DIY EDR is for stakeholders to talk to product companies, which by nature focus on products and what they do. Together, they stand up a proof of concept (POC) against a finite list of requirements and complete a purchase. As a result, organizations deploy standalone endpoint products, or attempt some level of basic integration with the rest of their security technology stack, but possibly without considering the big picture. Only a close look at EDR reveals the true scope of what goes into an efficient, effective EDR solution – and whether DIY or a managed EDR service is the better choice.
Let’s start by checking in on each component of EDR:
- Endpoint. Historically, the technology used for detection and response was managed by different departments, and each had different response motions. Now the common EDR approach is to bring all this diversity under one point of control – an effort that involves dozens of endpoint types: phones, tablets, servers, medical, industrial control systems (ICS), other IoT devices and so on. Endpoint variety and volume lead to complexity in asset discovery and EDR planning, implementation and support. The result? More complex activities on the endpoint from a single place (the EDR solution).
- Detection. In the past, detection was straightforward because things were good until something bad happened. Antivirus software quarantined the threat and cleaned up the issue. Now, effective detection depends on understanding enemy activity quickly to determine what is the threat, how and where it is moving, and how dangerous and widespread it is. Detection has become more about finding the abnormal or unusual versus the known bad.
- Response. Response involves what to do and when and how to do it. Various factors have to be considered before taking action. For example, the time of day (is this normal or abnormal behavior?) and the business impact of “catching” and provoking a bad actor. Perhaps the bad actor should be observed as it moves around to learn more about it before taking action. And, while the industry is well into automating responses, your organization may prefer that certain responses are manual.
Top Influencers of EDR Efficiency and Effectiveness
Efficiency and effectiveness come down to people, process and technology (PPT). But when EDR decisions are based primarily on product capabilities, tool overload can happen quickly, throwing off the PPT balance. Additionally, product-based decisions may not take into account the following topics that influence EDR success:
- The industry in which you and your customers operate. Healthcare has medical devices. Manufacturing has valves, pumps, and ICS. Journalists use devices to file their stories. Schools provide laptops or students bring their own devices. Given this variety, it’s important to think about the nature of your endpoints and what you are protecting. And to know which critical assets are located on which endpoints. You might store IP on servers, but IP also can reside on factory floor devices. If you have legacy technology, where is it and what is it doing? Substantial discovery work should precede EDR decisions. EDR is a case study in “know yourself” from a technology and data perspective.
- Risk assessment and profile. EDR decisions, like all security decisions, are better when they reflect your risk tolerance. If your stakeholders aren’t on the same page about risk, it’s difficult to set a baseline against which outcomes and value can be measured.
- Understanding your organization structure and stakeholders. Silos are the No. 1 cause of EDR failure. IT and SecOps may not be aligned. Some IT professionals, for example, are hesitant to add endpoint agents because they’re concerned about performance, while SecOps likely views agents as a necessity. Or, some stakeholders are uncomfortable with automated responses and their potential impact on the business. While you clearly want to stop a zero-day attack in its tracks, you may need to negotiate a gray zone of manual versus automated response actions. Part of this negotiation may be your bring-your-own-device (BYOD) policies and user reluctance to have software added to their devices. Don’t underestimate the nuances and politics of EDR. They are an important part of the calculus related to solution deployment and, ultimately, its effectiveness.
- Knowing which attackers, tactics, and techniques are most relevant to your business and industry. Some industries are in the sights of attackers based in certain countries. The nature of your critical assets attracts certain types of bad guys. Threat actor motivations also influence their choice of targets. For example, ransomware is financially motivated. If it is a top threat to your business and industry, speed is crucial. Before implementing EDR, you’ll want to combine knowledge of your endpoints with intelligence about who are your enemies and how they operate.
- Discovery of all endpoints. If legacy operating systems and hardware versions aren’t documented entities, you won’t know they exist. As a result, risk increases due to unknown vulnerabilities that attackers can exploit to get in the door. EDR only works when it’s deployed across most or all of the enterprise. Think “herd immunity.”
- The scope of your detection capability. Detection used to be a standalone, device-specific activity. An alert happened, and it was dealt with. Now singular device detection isn’t sufficient. You need to be able to detect new, novel threats and suspicious user behavior. Technologies such as SIEM; user behavior analytics (UBA); security orchestration, automation and response (SOAR); and breach simulation are increasingly viewed as necessary elements of defense. SOAR, for example, enables automated playbooks that speed response, and breach simulation tests the efficacy of your defenses.
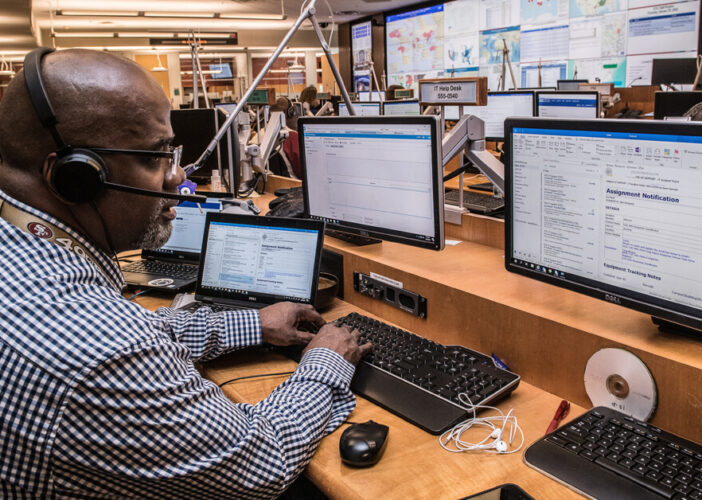
- In-house detection and response capabilities. Gone are the days of dark weeknights and weekends. You can’t shut off the lights on Friday night and come back on Monday to see what happened. Today’s attackers operate much faster than before. 24x7x365 monitoring should be supported by humans in a security operations center (SOC) and/or supplemented with SOAR.
- EDR solution evolution and scalability. Regardless of the size of your organization, the EDR solution you need today will need to adapt to keep up your defenses against an ever-changing threat landscape. Will your endpoints support new software? Are you able to implement a new endpoint solution on legacy factory floor devices or older energy systems? Identifying potential obstacles before you evaluate EDR solutions will improve your vetting process.
To DIY or Not to DIY?
If you run EDR internally, it’s a good idea to compare your solution to the latest recommended best practices to see how it stacks up. The checklist below also serves as a quick reference that may be useful in conversations with stakeholders.
| Not Part of Our EDR Solution | Confidence Level 1 (Low) to 5 (High) |
DIY Endpoint Detection and Response |
| EDR decisions are guided by a risk profile
|
||
| Organizational structure and stakeholders are well understood
|
||
| Industry sources and feeds provide information about new and emerging zero-day threats
|
||
| SIEM
|
||
| Integrated threat intelligence
|
||
| Artificial intelligence/machine learning capability
|
||
| Industry analyst perspectives on EDR solutions
|
||
| Ability to isolate endpoints when required
|
||
| Ability to monitor and scan 24x7x365
|
||
| Entire environment and all endpoints are discovered and visible
|
||
| Use of strong heuristics
|
||
| Data modeling
|
||
| Ability to keep up with alerts and response with current staff and skills
|
||
| Automated workflows
|
||
| Automated playbooks
|
||
| Have the necessary cybersecurity people and skills
|
||
| Ability to conduct threat analysis to the desired depth and breadth
|
||
| Single portal/dashboard to manage EDR
|
||
| Use of the latest EDR software
|
||
| Ability to do forensics
|
||
| User behavior analysis software
|
||
| Breach simulation capability
|
||
| Ability to scale as new endpoints are added
|
||
| Forensics for deep investigation
|
||
| Ability to set response rules for manual or automated response
|
||
| Adequate bandwidth to support endpoint data and image collection
|
||
| Includes insurance or breach coverage
|
||
| Is approved by our insurance provider per our policy
|
Choosing Your EDR Narrative
Whether you prefer a DIY approach and work with product vendors or engage a managed EDR service provider, validate credentials. Cybersecurity is complex, and vendors should help you reduce complexity, not add to it. Ask about market share, the length of time they’ve been in the market and outcomes for similar customers (industry, size, geographical presence). Be sure EDR is a primary focus, not a “oh yes, we do that, too” offering. If a POC or evaluation period is available, what is its scope? If your organization has a thousand endpoints, and a POC involves 10 or 20, you likely won’t have enough information to validate scalability or anticipate issues.
EDR has different narratives and outcomes. Both are tied to the discovery you do upfront to understand your environment, objectives, critical assets, staff capabilities, risk tolerance, security capabilities and so on. In our perspective, working through the top influencers listed above is the best way to optimize EDR efficiency and effectiveness.
Contact us to discuss EDR or the checklist or to explore your requirements and learn more about managed EDR.